When life at the forefront of Data security feels treacherous!
Playing the game of Ransomware…whether you like it or not
Does managing your data security sometimes feel like you are part of the Squid Game? Where any wrong move can have disastrous consequences?
Today we take a look at the villains in the world of the Cloud – the malicious actors who use various types of ‘ware’ to extort ransoms from their victims.

Here are some examples of type of attacks:
| Locker | Blocks access to computers and attackers require payment to unlock access. |
| Crypto | Encrypts all or some files on a computer, and attackers require payment before handing over an encryption key. Usually spreads via infected email attachments. |
| Double extortion | When cybercriminals demand one payment to decrypt the files and another not to make them public. |
| Ransomware as a service (RaaS) | When cybercriminals can access malicious code for a fee. |
While attacker’s methods have change over the years, the goal remains the same – target vulnerable victims, block access to important data, and demand a ransom to reinstate access again.
The Ransomware Industry has evolved rapidly from where it started and is now a multibillion-dollar industry.
| 1989 | The beginning of ransomware, with malware dubbed the AIDS Trojan. |
| 2000’s | The emergence of the internet and email brought GPCode and Archievus phishing attacks. |
| 2010 | Ransomware goes mainstream with locker ransomware, stronger encryption algorithms, and the concept of cryptocurrency. |
| Mid 2010’s | New targets are set and attacks move from PC to mobile, Mac, and Linux devices. |
| Late 2010’s | Ransomware goes global as techniques evolve to more sophisticated encryptions. |
| Late 2010 to early 2020 | Ransomware reaches its most destructive stage. Two factors have shaped this phase- extortionware and big-game hunting. |
| 2020 | The global Covid-19 pandemic also propelled the spread of double and triple extorsion variants, as well as RaaS. |
Ransomware is a business driven by economics, where operators are profit driven and face stiff competition and are using technology to increase access to your assets.
Now, more than ever, it is important to look at your defense and security strategy when it comes to your data.
There are many Malware strains, but below are some to know:
| BadRabbit | Encrypts the user’s file tables and demands Bitcoins to decrypt them. |
| Ryuk | Distributed by phishing emails containing malicious Microsoft Office documents. |
| Petya | A type of crypto-ransomware virus targeting Windows servers, laptops, and PCs in particular. |
| NotPetya | Considered ransomware, but as wiperware, it focuses on destroying files rather than collecting money. |
| Scareware | Generally tries to freak the users out by displaying an alarming message and consequently tricks them into downloading malware. |
| Jigsaw | Encrypts and progressively deletes files until a ransom is paid. |
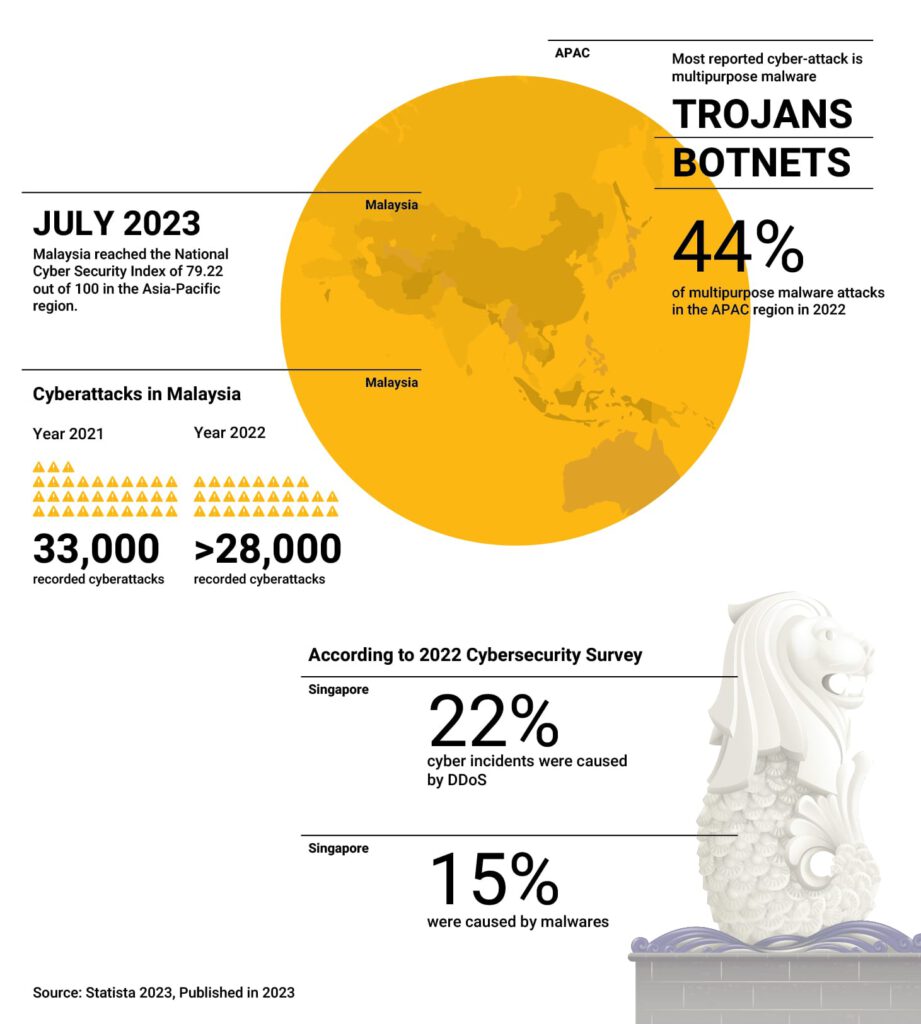
A Glance at Ransomware Statistics in the APAC Region